01.Overview
What is Remote Access V-Client?
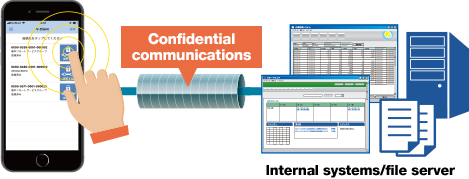
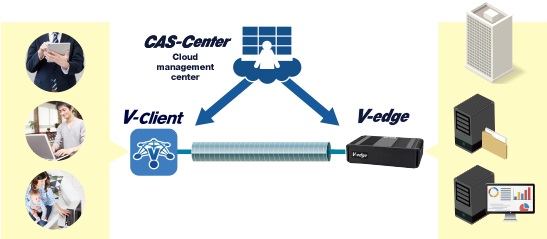
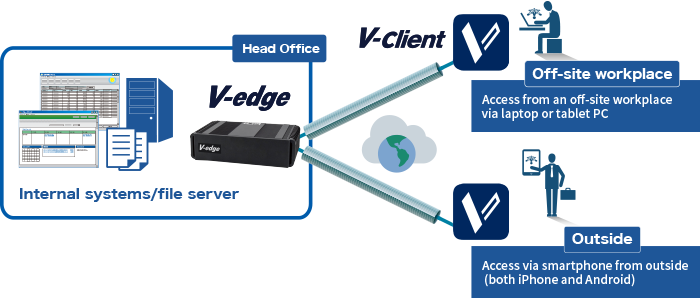
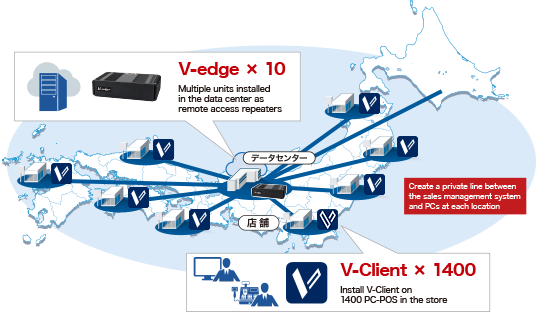
V-Client is remote access software used for connecting to a corporate network or cloud from home or on the go.
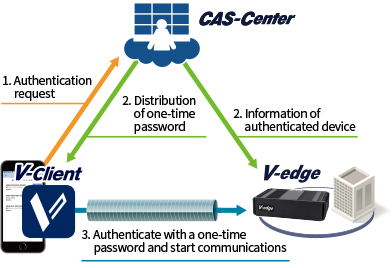
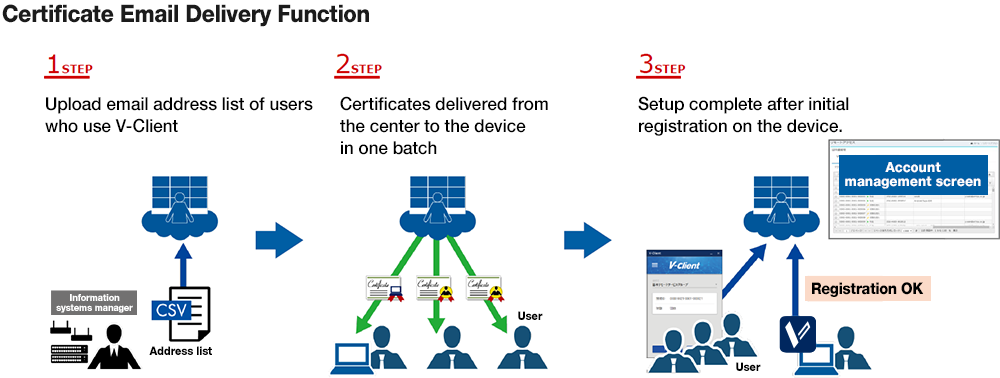
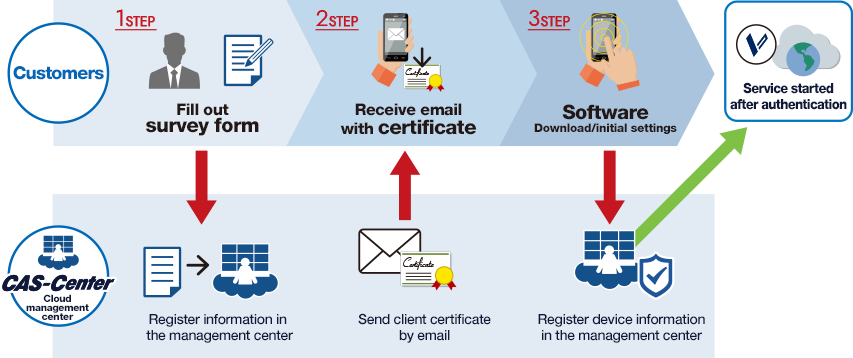
Certificates required for authentication are managed at the Management Center on the cloud.
Users can rely on the safety of the in-house portal and business apps, whether at home or on the go.

Remote Access Operations and Management Service for Customers
The Management Center handles remote access settings and operations.
-

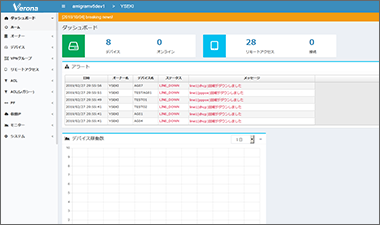
Centralized Management
- Initial settings / installation / and construction
- Adding / changing settings
- Issuing and suspending certificates
-

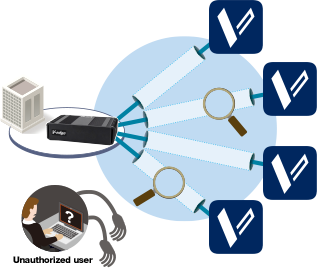
Communications Stability and Security
- Security settings on behalf of the customer
- Address disconnect / delay issues
- Record / storage connection logs
-

Operations Maintenance / Failure Recovery
- Automatic firmware updates
- Isolate line / router faults
- Send replacement equipment in case of equipment failure (send-out, send-back)